Have you ever sat across from a friend or a client and tried to explain the complexities of cloud computing, only to watch their eyes glaze over? The moment terms like Virtual Private Cloud, subnets, or NAT Gateways enter the conversation, the connection is often lost. It feels like trying to explain quantum physics using only a deck of cards. Using an aws forest analogy allows us to transform abstract, intimidating digital concepts into a tangible, lived experience that anyone can visualize.

Setting the Scene: The Vastness of the Digital Jungle
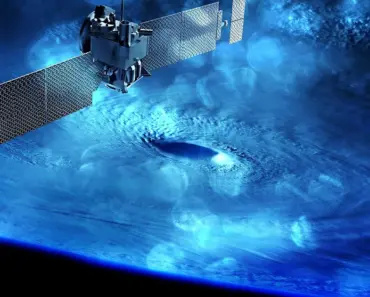
Imagine standing at the edge of a massive, ancient, and infinitely expanding forest. This isn’t just any forest; it is a living, breathing ecosystem that contains every resource imaginable. In this scenario, the forest represents the entire Amazon Web Services (AWS) ecosystem. It is vast, it is powerful, and it is nearly impossible to navigate without a map. When you first enter this environment, the sheer scale can be overwhelming. You see endless trees, winding rivers, and various types of terrain, much like how a developer sees hundreds of different services when they first log into the AWS Management Console.
To survive and thrive in this jungle, you cannot simply wander aimlessly. You need a designated space where you can build something permanent. You need a territory that belongs specifically to you, where you can control who enters and what happens inside. In the world of cloud computing, this is where we establish our foundation. We are not just looking for a single tree; we are looking to claim a specific plot of land where we can build a home, protect our belongings, and host our family.
This plot of land is your Virtual Private Cloud, or VPC. Think of the VPC as your private, fenced-off estate within the larger forest. While the forest is public and shared by everyone, your VPC is an isolated section where you define the boundaries. Within this estate, you decide where the roads go, where the houses sit, and how much privacy you require. This isolation is the cornerstone of cloud security, ensuring that your digital assets are not just floating loosely in the wild, but are contained within a structured, controlled environment.
Defining Your Boundaries with CIDR
Before you can build, you must define the size of your estate. In networking, we use something called Classless Inter-Domain Routing, or CIDR, to determine the range of addresses available to us. In our forest analogy, think of CIDR as your zip code or the specific range of coordinates that define your property line. If you claim a large block of coordinates, like 10.0.0.0/16, you are essentially saying, “Everything from this point to that point belongs to my estate.”
This range gives you a mathematical way to assign a unique “address” to every single thing you build inside your VPC. Whether it is a small shed, a massive mansion, or a simple garden path, every item needs an address so that the “delivery drivers” of data packets know exactly where to go. Without this structured addressing system, your forest estate would descend into chaos, with data wandering aimlessly through the trees, unable to find its destination.
Building the Home: Subnets and the Two-Story Structure
Once your estate is claimed, it is time to build. A single, massive building is often difficult to manage and secure. Instead, it is much more efficient to divide your property into different functional zones. In a VPC, we do this by creating subnets. A subnet is essentially a smaller subdivision of your larger network, allowing you to group related resources together and apply different rules to each group.
To make this easy to visualize, let’s imagine building a two-story house within our forest estate. This house will serve as our primary hub of activity, and its design will dictate how people and information move through our digital world. We will use the concept of public and private subnets to manage our security and accessibility.
The Ground Floor: The Public Subnet
The ground floor of our forest house is designed for interaction. This is our Public Subnet. Imagine a bright, welcoming area with a large front porch and an open door. This area is meant for guests, visitors, and delivery people. In technical terms, resources placed in a public subnet are reachable from the internet. This might include a web server that hosts your company’s website or a load balancer that directs incoming traffic.
Because this floor is open to the outside world, it requires careful management. You wouldn’t leave your jewelry box sitting on the coffee table in a room where anyone can walk in off the street, right? Similarly, in a public subnet, you only place the specific components that absolutely must be exposed to the internet. Everything else stays tucked away on the level above.
The Upper Floor: The Private Subnet
The second floor of our house is the Private Subnet. This area is strictly for the family. There are no front doors leading directly from the forest to this floor; the only way to reach it is through the internal staircase of the ground floor. This floor is where we keep our most sensitive assets, such as databases containing customer information or internal application logic that should never be touched by a stranger.
By separating our house into these two levels, we create a natural layer of defense. Even if a stranger manages to walk onto the front porch (the public subnet), they are still physically separated from the private living quarters (the private subnet) by the structure of the house itself. This architectural separation is a fundamental principle of secure cloud design, ensuring that a breach in one area does not automatically grant access to the entire estate.
The Double Fence System: Protecting the Estate
Even with a well-designed house, living in a wild forest requires robust security. We cannot rely solely on the walls of our home to keep us safe from the unpredictable elements of the jungle. We need a multi-layered defense strategy. In the aws forest analogy, we implement a “double fence” system to ensure that only authorized entities can interact with our resources.
This approach, often called defense-in-depth, means that if one security measure fails, another is already in place to catch the intruder. We use two distinct types of barriers: one at the perimeter of our subnets and another surrounding our individual family members. These are known as Network Access Control Lists (NACLs) and Security Groups.
The Outer Boundary: Network Access Control Lists (NACLs)
The first line of defense is the outer fence that surrounds the entire perimeter of our property or a specific zone (the subnet). This is the Network Access Control List, or NACL. Imagine a tall, sturdy wooden fence with a gatekeeper standing at the entrance. This gatekeeper checks every single person or animal trying to enter or leave the property. If you aren’t on the approved list, you aren’t getting in.
One critical technical detail about NACLs is that they are “stateless.” In our analogy, this means the gatekeeper has a very short memory. If a guest enters through the gate, the gatekeeper doesn’t automatically remember them. When that guest tries to leave, the gatekeeper checks the list all over again. If there isn’t a specific rule allowing that person to exit, they will be blocked, even if they were just inside a moment ago. This requires you to be very explicit with your rules, defining both who can come in and who is allowed to go out.
The Inner Sanctum: Security Groups
The second line of defense is much more personal. While the NACL protects the entire yard, Security Groups act like individual fences around each specific room or person in the house. If the NACL is the perimeter fence, the Security Group is the locked door to your bedroom. Even if someone manages to get past the outer gate and into the yard, they still cannot enter your room unless they have the specific key for that door.
Unlike the gatekeeper at the main fence, Security Groups are “stateful.” This means they have a great memory. If you invite a guest into your room, the Security Group remembers that the interaction was authorized. When that guest wants to leave, the Security Group recognizes them and lets them out without asking for permission again. This makes managing individual resources much easier and more fluid, as you don’t have to write a rule for every single return trip of a conversation.
The Family Members: EC2 Instances and the Human Element
Now that we have our estate, our house, and our fences, it is time to meet the residents. The inhabitants of our forest home are the EC2 Instances, or Elastic Compute Cloud. To make this relatable, let’s imagine our family consists of five members. Each family member represents a virtual server—a unit of computing power that performs tasks, runs applications, and processes data.
Each family member is equipped with their own personal communication device, which in technical terms is a Network Interface Card (NIC). This allows them to send and receive information. Just as a person uses a phone to interact with the world, an EC2 instance uses its NIC to communicate with other servers, databases, and the internet. The “Elastic” part of EC2 means that our family can grow or shrink instantly. If we suddenly need to host a massive forest festival, we can instantly add ten more family members to help with the work. When the festival is over, they can depart, and we stop paying for their stay.
The Kids and the NAT Gateway
In our house, the children live in the private subnet on the upper floor. They want to be able to use the internet to do their homework or play games, but for safety reasons, we don’t want them having a direct connection to the outside world that strangers could use to find them. They need to be able to reach out, but the world shouldn’t be able to reach in.
To solve this, we install a NAT Gateway. Think of the NAT Gateway as a shared family hotspot or a single, secure communication window in the upper floor. The children can use this window to send messages out to the world. When they do, the NAT Gateway sends the message on their behalf, using its own “public” identity. When the response comes back, the gateway recognizes it belongs to the children and passes it up to them. This allows our private residents to enjoy the benefits of the internet without ever exposing their private room numbers or personal identities to the wild forest.
Navigating the Estate: Route Tables and the Master Blueprint
A house without hallways is just a collection of isolated boxes. To ensure that movement is efficient and that no one gets lost, we need a way to navigate. In our forest home, we rely on a master blueprint that dictates how every room connects to every other room and how the exits are located. In AWS, this is known as a Route Table.
You may also enjoy reading: 3 New iOS Features to Add to Popular iPhone Apps.
The Route Table is a set of rules that tells data packets exactly where to go. Imagine a packet of data is like a person walking through the house. The Route Table acts as the signage in the hallways. A sign might say, “To get to the kitchen, turn left at the stairs,” or “To reach the exit, go straight through the front door.” Without these signs, a person (or a piece of data) might wander into a closet and stay there forever, or end up in a restricted area by mistake.
Every subnet in your VPC is associated with a route table. By carefully designing these tables, you can control the flow of traffic with precision. You can ensure that traffic from the ground floor can reach the upper floor, but traffic from the outside can only reach specific designated areas. This level of granular control is what allows complex cloud architectures to function smoothly and securely.
Surveillance and Monitoring: CloudTrail and CloudWatch
Living in the middle of a vast forest requires constant vigilance. You need to know if someone is tampering with your fences, if a fire has started in the kitchen, or if a family member has left the stove on. In the cloud, we achieve this through two essential services: CloudTrail and CloudWatch. While they may sound similar, they serve two very different and equally vital purposes.
CloudTrail: The Security Camera System
CloudTrail is our comprehensive security camera system. It is installed in every hallway, every room, and every entrance of our estate. CloudTrail doesn’t care about the “temperature” of the house; it cares about actions. It records every single event: Who opened the front door? Who accessed the safe in the study? Who changed the settings on the security fence? It even records who logged into the house’s computer system.
This creates an immutable audit log. If something goes wrong—perhaps a valuable item goes missing—we can go back to the CloudTrail footage and see exactly what happened, at what time, and who was responsible. This is indispensable for security forensics and for maintaining compliance with industry standards. In the digital world, knowing “who did what and when” is the foundation of accountability.
CloudWatch: The Smart Alarm System
While CloudTrail watches the people, CloudWatch watches the environment. Think of CloudWatch as a sophisticated smart home system equipped with smoke detectors, thermometers, and motion sensors. It monitors the “health” and “performance” of our home. Is the kitchen getting too hot? Is the water pressure in the pipes dropping? Is the family using too much electricity?
CloudWatch collects metrics—numerical data points about the state of your resources. If a metric hits a certain threshold, such as the temperature rising above a safe level, CloudWatch can trigger an alarm. This alarm can then initiate an automated response. For example, if the “smoke detector” (a high CPU usage alarm) goes off, CloudWatch can automatically trigger an “emergency response” (launching more EC2 instances to handle the load). This automation allows your cloud estate to be self-healing and highly responsive to changing conditions.
The Storage Tiers: S3, EBS, and Glacier
Every family needs a place to keep their belongings, from the daily items like groceries to the precious heirlooms that are only brought out once a decade. In our forest home, we have implemented a three-tier storage system to manage our belongings efficiently, mirroring how AWS handles data.
EBS: The Household Closets
Elastic Block Store (EBS) is like the closets and drawers inside our house. These are high-speed, easily accessible storage spaces that are physically attached to our family members (the EC2 instances). If a family member needs a tool or a piece of clothing right now, they reach into the nearby closet. In technical terms, EBS provides block-level storage that is used by servers for their operating systems and active applications. It is fast, reliable, and always within arm’s reach.
S3: The Large Storage Shed
Sometimes, we have items that are too big for a closet, like a collection of outdoor gear or a large batch of supplies. For this, we have a large, organized storage shed located just outside the house. This is Simple Storage Service, or S3. S3 is object storage, meaning it is designed to hold vast amounts of unstructured data—photos, videos, backups, and documents. It is incredibly scalable; if we buy more gear, we simply expand the shed. It is also highly durable, ensuring that our belongings are safe from the elements.
Glacier: The Deep Underground Vault
Finally, there are the items we rarely ever touch, such as old family photo albums or legal documents from years ago. We don’t want to waste valuable space in the house or the shed on these. Instead, we keep them in a deep, climate-controlled underground vault located far from the main house. This is Amazon S3 Glacier. It is an archival storage service designed for long-term retention. It is much cheaper than the shed or the closets, but there is a catch: if you want to retrieve something from the vault, it takes time to go down there and bring it back up. This perfectly mirrors the trade-off in cloud computing between cost and retrieval speed.
Securing the Keys: KMS and Secrets Manager
As our estate grows, so does the complexity of our security. We can’t just rely on fences and cameras; we need to protect the very keys to our kingdom. In a modern digital environment, managing encryption and sensitive credentials is a massive challenge. If a family member loses a key or a password is stolen, the entire estate is at risk.
To prevent this, we use two specialized services: Key Management Service (KMS) and Secrets Manager. KMS is like a high-security locksmith that manages the master keys used to lock all our digital chests and files. It ensures that the keys themselves are kept in a vault that even the family members can’t easily access, providing a centralized way to manage encryption across the entire forest estate.
Secrets Manager, on the other hand, is like a highly secure, automated safe for our most sensitive passwords and codes. Imagine if every time a family member changed their password, a tiny robot automatically updated the password in every single lock in the house. That is exactly what Secrets Manager does through “auto-rotation.” It manages the sensitive credentials that our applications need to talk to each other, ensuring that even if a password is leaked, it will soon be useless because the robot has already changed it.
By using this aws forest analogy, we see that the cloud is not a mysterious, ethereal void. It is a structured, logical, and highly organized environment. Whether you are building a small cabin or a sprawling palace, the principles remain the same: define your boundaries, secure your layers, organize your paths, and monitor your environment. With the right blueprint, anyone can build their dream home in the digital forest.